Problem Description
This KB article addresses the following NRPE error:
NRPE - CHECK_NRPE: Received 0 Bytes From Daemon. Check The Remote Server Logs For Error Messages
Assumed Knowledge
The following KB article contains an explanation of how NRPE works and may need to be referenced to completely understand the problem and solution that is provided here:
NRPE - Agent and Plugin Explained
Troubleshooting The Error
First, make sure that NRPE is running as this is a common cause of this error. For instructions on how to do so, refer to the following KB article under Check the NRPE Service Status.
NRPE - CHECK_NRPE: Socket Timeout After n Seconds
The other causes of this problem all deal with arguments. If you are passing arguments to the remote host through NRPE, the argument usage should be consistent between the Nagios XI service check and the arguments declared in the command directive in the remote host's nrpe.cfg.
Additionally, check the remote host's nrpe.cfg for the dont_blame_nrpe directive. Take this command executed on the Nagios XI server as an example:
/usr/local/nagios/libexec/check_nrpe -H 10.25.13.30 -t 30 -c check_users -a '-w 5 -c 10'
The -a is the arguments that are being sent to the NRPE agent.
-
When dont_blame_nrpe=1, arguments will be accepted by the NRPE agent
-
This allows for dynamic commands, for example thresholds for warning and critical arguments can be adjusted on the Nagios XI server and nothing needs to be updated on the NRPE agent
-
However there is a risk that a potential security hole could be exploited (for example a malicious user could identify a way to delete all the files on the remote server)
-
-
When dont_blame_nrpe=0, arguments will be rejected by the NRPE agent
-
This means commands need to be specifically defined on the NRPE agent. If you wanted to adjust the thresholds for warning and critical arguments, these would need to updated on each the NRPE agent
-
This limits the potential of a malicious user being able to do bad things to the remote server, as "unknown arguments" are not accepted.
-
To identify what setting your NRPE server has defined, log into the remote host as the root user and execute:
grep -e ^dont /usr/local/nagios/etc/nrpe.cfg
The expected output will be something like:
dont_blame_nrpe=1
No Arguments
To verify if your argument usage is consistent, compare the check in Nagios XI to the command directive in the remote host's /usr/local/nagios/etc/nrpe.cfg file. If you have declared all the arguments for a check in the nrpe.cfg file, then Nagios XI should pass no arguments other than the command itself. In the example below, the command directive check_users is defined to not receive any arguments:
command[check_users]=/usr/local/nagios/libexec/check_users -w 5 -c 10
You can verify the the arguments which are sent to the remote host from Nagios XI by navigating to Configure > Core Config Manager > Services and select the check_user service (in this example).
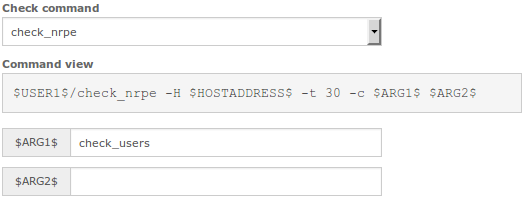
As you can see the service check is created to send no arguments other than the command name in $ARG1$:
check_command = check_nrpe
$ARG1$ = check_users
$ARG2$+ <blank>
Combined Arguments
This format encapsulates all of the arguments into one field in Nagios XI and one $ARG1$ in the remote host's nrpe.cfg file. This is how Nagios XI creates services configured through the Linux Server and NRPE wizards. If you compiled NRPE from source for the remote host but are using the XI wizards to create checks, you will have to edit the command directive in the remote host's nrpe.cfg file.
nrpe.cfg command directive:
command[check_users]=/usr/local/nagios/libexec/check_users $ARG1$
The service check is set up in Nagios XI:

check_command: check_nrpe
$ARG1$ check_users
$ARG2$ -a '-w 5 -c 10'
$ARG3$+ <blank>
You can see that check_nrpe sends everything in the $ARG2$ field. Remember the -a in the $ARG2$ field is how check_nrpe sends arguments to the NRPE client. Because the arguments are enclosed in 'single quotes' this is how the NRPE client receives this as $ARG1$.
Separate Arguments
If you have setup multiple arguments for each threshold/option, Nagios XI will pass them in the same order:
nrpe.cfg command directive:
command[check_users]=/usr/local/nagios/libexec/check_users -w $ARG1$ -c $ARG2$
The service check is set up in Nagios XI:

check_command: check_nrpe_arguments
$ARG1$ check_users
$ARG2$ 5
$ARG3$ 10
$ARG4$+ <blank>
Notice the command directive expects $ARG1$ for -w and $ARG2$ for -c even though in Nagios XI they are $ARG2$ and $ARG3$. This trips up beginners, this is because check_nrpe sends arguments after the -a, these are received by the NRPE client as $ARG1$, $ARG2$ and so on.
Take note that the Check Command in the screenshot above is a custom check command that has been defined. In the previous example the -a was part of the $ARG1$ variable. However in this example it was defined as part of the check command, which means you can put just the threshold values in $ARG2$ and $ARG3$.
All of these argument configuration methods are valid, though it is best to choose one method and stick to it for consistency and ease of troubleshooting.
Final Thoughts
For any support related questions please visit the Nagios Support Forums at:









